Defender for Endpoint Certificate IOC Block
This guide will show an administrator how to create a block of a specific application based on certificate association.
 Role Requirements
Role Requirements
Procedure Scope: Administrators
Required Group Membership: Admin.Security
Handbook Reference
Package: Device Security
Domain: Endpoint Indicator Management
Modifies: Blocked Certificates
![]()
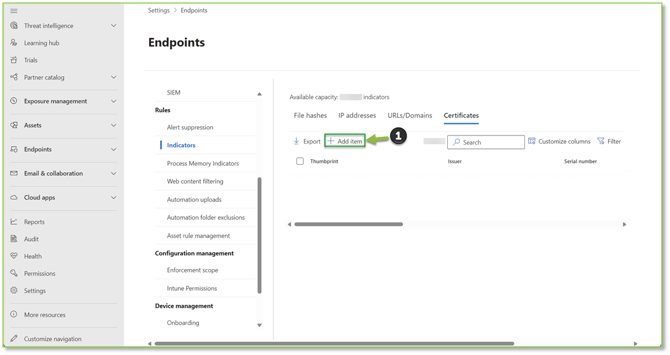
- Navigate to the Certificates – Microsoft Defender portal, locate and select the Add Item action.
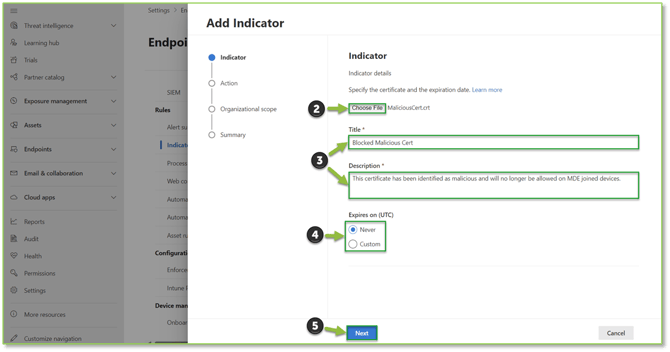
- A pop-up will be generated select the Chose File action to upload the malicious certificate. You will also need to provide basic information associated with the entry such as Title and Description, with the intent of giving future context if the rule is to be reviewed later. From this page you will either keep the default block time frame of Never or specify a Custom time frame. Select Next to continue.
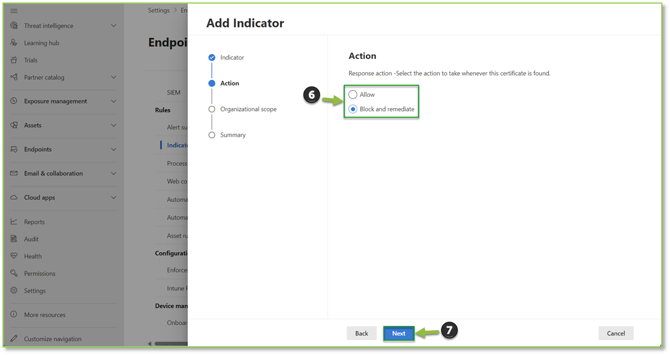
- For the response action, select Block and Remediate. This will block the certificate, along with taking automated response against the file if found, such as removing the file depending on how the Microsoft automated response goes. Select Next to continue.
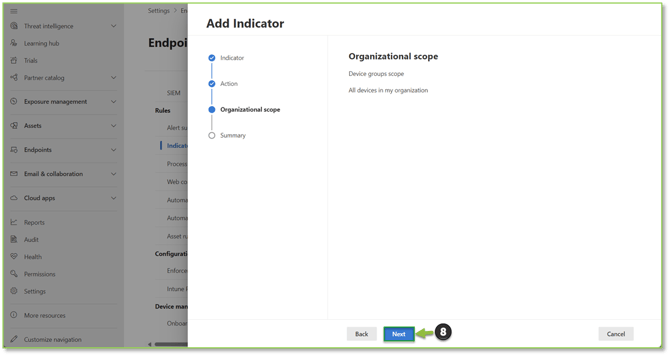
- The default for the organizational scope is set to all MDE joined devices, select Next to continue.
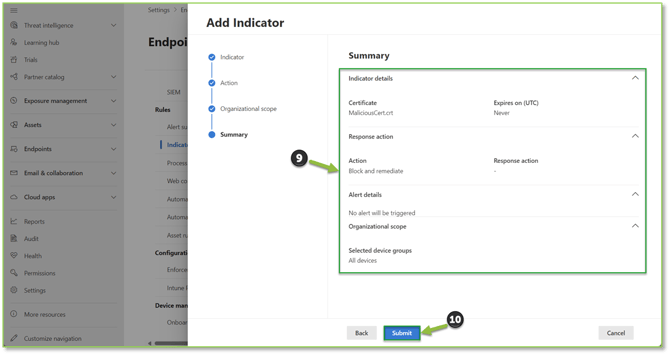
- The summary page will allow you to see all configured settings for the indicator, if you detect a discrepancy at this stage make note of the section and select Back to go to the previous sections to make the necessary alterations before finalization. If everything checks out, select Submit to publish the indicator.
Need Assistance?
Reach out to your Customer Success Manager to discuss how a Sittadel cybersecurity analyst can assist in managing these tasks for you. New to our services? Inquire about arranging a consultation to explore optimizing your Azure environment for painless management.
.png?width=190&height=95&name=Sittadel%20Header%20Logo%20(2).png)
