Monitor & Respond - Email Alert & Incident Queue
 Role Requirements
Role Requirements
Procedure Scope: Administrators
Required Group Membership: Admin.SecurityOperator
 Handbook Reference
Handbook Reference
Package: Email Security
Domain: Alert & Incident Queue
Modifies: Email Alert Queue, Email Incident Queue
When to Perform this Operation
Twice a day: Key times such as 8am and 2pm.

Analyst Description and Importance
The Defender Incident and Alert Queue is used to monitor essential actions and metrics for the organizations email security and health. It provides the centralized place where security events are organized and prioritized for review, empowering analysts to respond and take action on potential security or business impacts. Continuously monitoring the queue not only ensures that email threats are being addressed and managed effectively, but also that the organization is aware of any events that could impact delivery or availability of email.
Security Importance:
Monitoring and responding to the alert & incident queue ensures any interruptions to email security are resolved, helping to mitigate the security of risk of critical email security functions from being impaired due to a system change or alert that has been overlooked.
Business Importance:
Monitoring and responding to the alert & incident queue ensures any interruptions email deliverability are resolved, helping to mitigate the business risk of critical email not being delivered due to a system change or alert that has been overlooked.
Covered in this Operation
Train
- Understanding Alert Entries
- Understanding Incident Entries
- Understanding Email Detection Technologies
- Routine Normal-Urgency Alert Resolution
- Response to High-Urgency Alerts
Monitor
- Review the Defender for Email Alert Queue
- Review the Defender for Email Incident Queue
Respond
- Respond with Alert Resolved
- Respond with Incident Resolved
In email alert and incident management, training is essential for developing a solid understanding of what each alert and incident represents, beyond just hitting "resolve." Effective training enables analysts to interpret the significance of alerts, understand how incidents are constructed, and gain insight into the detection technologies behind them.
With this knowledge, analysts can make informed decisions on when to respond, investigate, or simply resolve an alert. This isn’t about overcomplicating the process—it’s about ensuring that actions are taken with the right context, improving efficiency and accuracy without unnecessary steps. Proper training means analysts can manage alerts and incidents effectively, addressing issues with confidence and minimizing missed risks.
Understanding Alert Entries
In Microsoft Defender, understanding alert details is critical for analyzing and responding to email-based threats and functionality impacts. Each alert is composed of multiple sections that convey essential information about the detected issue and its context.
Alert Queue Entry
- Alert Name: The title of the alert that summarizes the nature of the security event, such as “Email Sending Limit Exceeded” or “Email Reported by User as Junk”. This name gives analysts a quick overview of what type of issue has been identified.
- Tags: Custom labels added to alerts for easy categorization, filtering, or prioritization. Common tags might include “High Priority,” “Phishing,” or specific departmental labels. These tags help organize alerts, making it simpler to sort and focus on relevant alerts.
- Severity: The impact level of the alert, such as “Informational”, “Low”, “Medium”, or “High”. This rating helps analysts prioritize their responses based on the potential risk to the organization. Higher severity alerts generally require immediate investigation.
- Investigation State: The current status of the investigation for the alert, such as “Queued”, “No Threats Found”, “Pending Action”, or “Remediated“. This state provides visibility into which alerts have already been addressed or need further attention.
- Status: The current condition of the alert, such as “New”, “In Progress”, or “Resolved”. The status shows the life cycle of the alert, helping analysts identify unresolved alerts that may still pose a threat.
- Category: The type of threat associated with the alert, such as “Threat Management”. The category allows analysts to filter and organize alerts by threat type, making it easier to manage specific email threats more efficiently.
- Detection Source: Identifies the Microsoft Defender component that generated the alert, typically listed as Defender for Office 365 (MDO) for email alerts. This field helps analysts understand where the alert originated, guiding them to the right tools and resources for investigation.

Alert State section:
- Classification: Defines the nature of the threat after analysis, categorizing it as "True Positive", "Informational", or "False Positive". Helps categorize alerts for post-remediation activities.
- Assigned to: Specifies the analyst or team which was/is responsible for taking an action on the alert. Ensures accountability and clear ownership on response actions.

Alert Details section:
- Category: Describes the general type of alert, such as “Threat Management” or “Compliance Manager”. Assists in determining the system the alert relates to and was triggered from.
- MITRE ATT&CK Techniques: Lists the specific techniques associated with the alert from the MITRE ATT&CK framework. Provides a standardized way to understand and communicate threat behaviors.
- Detection Source: Identifies which aspect of the Defender stack the alert originated from, such as "Microsoft Defender for Office 365" or “Microsoft Defender for Endpoint”. Indicates the initial detection source.
- Service Source: Specifies the Microsoft 365 service involved, like "Office 365". Adds data similar to detection sources on which service the threat is associated with.
- Detection Technology: Describes the method or technology used to detect the threat, such as "General Filter", “File Detonation", or "IP Reputation". Offers insight into which detector determined malicious behavior.
- Generated On: Provides the date and time when the alert was created by the system. Important for establishing the timeline of events.
- First Activity: Indicates the earliest timestamp of the suspicious activity related to the alert. Helps determine how long the threat has been present and will always precede the “Generated On” field.
- Last Activity: Indicates the latest timestamp of the suspicious activity related to the alert, either as a result of the threat being remediated or the threat becoming inactive. Helps determine the time between detected activity and remediation/inactivity of the threat by measuring delta between “First Activity” and “Last Activity”.

Evidence section:
- Evidence Entries: Lists specific data points supporting the alert, such as suspicious emails, IP’s, devices, links, or attachments. Serves as the basis for tracking affected types of entities and their remediation status.

Alert Description section:
- Alert Description: Provides a detailed summary of the alert, explaining the nature of the threat and potential impact. Essential for understanding the context and severity.

Alert Policy section:
- Policy Name: Specifies the name of the security policy that triggered the alert, such as "Anti-Phishing Protection Policy", if present. Links the alert to specific organizational controls.
- Alert Policy ID: The unique identifier associated with the alert policy. Facilitates tracking and reference to policy documentation.

Incident Details section:
- Incident: References the incident number linked to the alert for tracking and correlation purposes. Integrates the alert into broader incident management processes.
- Incident Severity: Indicates the level of risk associated with the incident, such as "High", "Medium", or "Low". Guides the urgency and extent of response actions.
- Active Alerts: Shows the number of active alerts associated with the incident. Provides an overview of the incident's scope.
- Devices: Lists any affected devices, if applicable. Important for identifying compromised endpoints.
- Users: Identifies users impacted by the threat. Necessary for user-specific remediation and communication.
- Mailboxes: Specifies the mailboxes that were targeted or affected. Key for addressing email-based threats.
- Apps: Lists any applications involved in the incident, if applicable. Helps in assessing the vulnerability of software and services.

Impacted Assets section:
- Devices (May Appear): Details the specific device entries as they relate to a single alert, with these individual entries that can be found per-alert feeding the overall impact reflected in an incident.
- Users (May Appear): Details the specific user entries as they relate to a single alert, with these individual entries that can be found per-alert feeding the overall impact reflected in an incident.
- Mailboxes (May Appear): Details the specific mailbox entries as they relate to a single alert, with these individual entries that can be found per-alert feeding the overall impact reflected in an incident.
- Apps (May Appear): Details the specific app entries as they relate to a single alert, with these individual entries that can be found per-alert feeding the overall impact reflected in an incident.
- Cloud Resources (May Appear): Details the specific cloud resource entries as they relate to a single alert, with these individual entries that can be found per-alert feeding the overall impact reflected in an incident.

Comments and History section:
- Comments Section: Allows analysts to add notes and document actions taken or observations about the alert. Facilitates communication among team members and maintains a record of investigative steps.
- History Log: Displays a timeline of actions related to the alert, such as changes in status and assignments to different analysts. Automation events are also tracked here, like linking the alert to a specific incident.

Understanding Incident Entries
In Microsoft Defender, understanding how alerts inform incidents is critical for analyzing and responding to threats and functionality impacts. Each incident is composed of multiple alerts, with a critical understanding being that an incident will never exist without an alert but instead acts as a vehicle to provide context for one or more alerts.
Attack Story section:
- Alerts: Lists all alerts that are part of the incident, providing a consolidated view of related security events and showing how individual alerts contribute to the overall incident.
- Incident Graph: A visual representation of the relationships between entities involved in the incident, such as users, devices, files, and network connections. Displays the attack's progression and identifies patterns or correlations among different components.

Alerts section:
- Alert Name: The title of the alert that summarizes the nature of the security event, such as "Email Sending Limit Exceeded" or "Phishing Attempt Detected." Provides a quick overview of the identified issue.
- Tags: Custom labels added to alerts for easy categorization, filtering, or prioritization. Common tags might include “High Priority,” “Phishing,” or specific departmental labels. These tags help organize alerts, making it simpler to sort and focus on relevant alerts.
- Severity: The impact level of the alert, such as “Informational”, “Low”, “Medium”, or “High”. This rating helps analysts prioritize their responses based on the potential risk to the organization. Higher severity alerts generally require immediate investigation.
- Investigation State: The current status of the investigation for the alert, such as “Queued”, “No Threats Found”, “Pending Action”, or “Remediated“. This state provides visibility into which alerts have already been addressed or need further attention.
- Status: The current condition of the alert, such as “New”, “In Progress”, or “Resolved”. The status shows the life cycle of the alert, helping analysts identify unresolved alerts that may still pose a threat.
- Category: The type of threat associated with the alert, such as “Threat Management”. The category allows analysts to filter and organize alerts by threat type, making it easier to manage specific email threats more efficiently.
- Detection Source: Identifies the Microsoft Defender component that generated the alert, typically listed as Defender for Office 365 (MDO) for email alerts and Microsoft Defender for Endpoint for endpoint alerts. This field helps analysts understand where the alert originated, guiding them to the right tools and resources for investigation.

Assets section:
- Devices: Details specific devices involved in the incident, including endpoints that may have been compromised or used in the attack. Provides information crucial for isolating affected devices and preventing further spread.
- Users: Information about users associated with the incident, such as those who received phishing emails or whose accounts may have been compromised. Identifies impacted users for targeted remediation efforts.
- Mailboxes: Details of mailboxes involved in the incident, important for email threats where specific mailboxes have been targeted or affected. Assesses the extent of the threat within the organization's email infrastructure.
- Apps: Information about applications involved in the incident, which may include cloud apps or on-premises software that have been exploited or are at risk. Helps in securing application environments and data.
- Cloud Resources: Details about cloud resources related to the incident, such as Azure services or other cloud assets that may have been involved. Protects cloud infrastructure and services from ongoing threats.

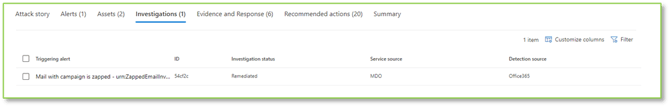
Investigations section:
- Triggering Alert: The initial alert that prompted the automated investigation, serving as the starting point for analyzing the incident. Highlights the event that first signaled a potential threat.
- ID: The unique identifier assigned to the investigation, used for tracking, and referencing throughout the incident response process.
- Investigation Status: The current state of the automated investigation, such as "Pending Action", "Remediated", or "Failed". Indicates progress and whether further manual intervention is required.
- Service Source: Specifies the Microsoft 365 service involved, like "Office 365". Adds data similar to detection sources on which service the threat is associated with.
- Detection Source: Identifies the Microsoft Defender component that generated the alert, typically listed as Defender for Office 365 (MDO) for email alerts. This field helps analysts understand where the alert originated, guiding them to the right tools and resources for investigation.
Evidence and Response section:
- Emails (May Appear): Lists emails that are evidence in the investigation, including malicious messages, phishing attempts, or emails with suspicious attachments or links. Outlines individual emails and if they are in scope for remediation actions, should they be approved.
- Email Clusters (May Appear): Groups of related emails identified as part of the same threat campaign. Outlines the email clusters with their status and if they are in scope for remediation actions, should they be approved.
- IP Addresses (May Appear): IP addresses involved in the incident, either as sources of malicious activity or as targets. Outlines IP addresses with their status and if they are in scope for remediation actions, should they be approved.
- Files (May Appear): Files pertinent to the investigation, such as malware samples, infected documents, or unauthorized downloads. Outlines files with their status and if they are in scope for remediation actions, should they be approved.
- Processes (May Appear): Processes running on devices associated with the incident, which may indicate malware execution or unauthorized activities. Outlines processes with their status and if they are in scope for remediation actions, should they be approved.
- URL’s (May Appear): Web addresses involved in the incident, such as phishing sites, command-and-control servers, or sites hosting malware. Outlines URLs with their status and if they are in scope for remediation actions, should they be approved.

Recommended Actions section:
- Rank: The priority level assigned to each recommended action, guiding which steps to take first based on their potential impact on mitigating the threat.
- Recommended Action: Specific steps suggested to help prevent future threats of this type, such enforcing MFA or enabling other specific security controls.
- Score Impact: The number of points converted to a percentage of total possible points given to an organizations Secure Score for implementing the recommendation.
- Points Achieved: The number of points towards the total possible points given to an organizations Secure Score for implementing the recommendation.
- Status: The current state of the recommended action, such as "Completed” or “To Address”, based on if the Secure Score observes the expected configuration items already in place.

Understanding Email Detection Technologies
As it pertains to alerts and incidents for email, the detection technologies are mirrored in the same way as in the quarantine queue and reflect identically. For Microsoft’s verbatim definitions of these, view the knowledge article here.
Detection |
Technology |
Investigation Goal |
||
Advanced Filter |
Phishing signals based on machine learning. |
Review the Email Details for discrepancies in sender information. |
||
Campaign |
Messages identified as part of a campaign. |
Check the Campaign ID in the Email Details to assess if it's part of a suspicious or known bad campaign. |
||
File Detonation |
Safe Attachments detected a malicious attachment during detonation analysis. |
Inspect the Attachments section for listed threats and detection technologies used. |
||
File Detonation Reputation |
File attachments previously detected by Safe Attachments detonations in other organizations. |
Examine Attachments for threat labels and malware families associated with the files. |
||
File Reputation |
The message contains a file that was previously identified as malicious. |
Analyze the Attachments for any known malicious indicators or malware types. |
||
Fingerprint Matching |
The message closely resembles a previously detected malicious message. |
Compare the message to observed threat patterns in the Email Details. |
||
General Filter |
Phishing signals based on analyst rules. |
Scrutinize the Email Details and Quarantine Details for typical phishing indicators like spoofed sender info. |
||
Domain Reputation |
Domain sending message known for spam or phishing. |
Scrutinize the Email Details and Quarantine Details for typical phishing indicators like spoofed sender info. |
||
Impersonation Brand |
Sender impersonation of well-known brands. |
Examine if the sender is attempting to appear similar to a known brand in the Email Details. |
||
Impersonation Domain |
Impersonation of sender domains that you own or are specified for protection. |
Examine if the sender's domain is attempting to appear similar to one of the organizations domains in the Email Details. |
||
Impersonation User |
Impersonation of protected senders specified in anti-phishing policies. |
Investigate if the sender information is attempting to appear similar to an internal user the Email Details. |
||
Mailbox Intelligence Impersonation |
Impersonation detections from mailbox intelligence. |
Review the Email Details for patterns that match known impersonation tactics. |
||
Mixed Analysis Detection |
Multiple filters contributed to the message verdict. |
Conduct a comprehensive cross-section review of Email Details, Quarantine Details, URLs, and Attachments. |
||
Spoof DMARC |
The message failed DMARC authentication. |
Confirm DMARC status in Email Details and assess for spoofing risks. |
||
Spoof External Domain |
Sender email address spoofing using a domain that's external to your organization. |
Examine if the sender's domain is attempting to spoof an external organizations domain in the Email Details. |
||
Spoof Intra-org |
Sender email address spoofing using a domain that's internal to your organization. |
Examine if the sender's address is attempting to spoof an internal user to the organization in the Email Details. |
||
URL Detonation |
Safe Links detected a malicious URL in the message during detonation analysis. |
Scrutinize the URLs listed in the URLs section for malicious links or unusual redirect behaviors. |
||
URL Detonation Reputation |
URLs previously detected by Safe Links detonations in other organizations. |
Investigate the URLs for previous threats and confirm their reputation with URL scanning tools. |
||
URL Malicious Reputation |
The message contains a URL that was previously identified as malicious. |
Investigate the URLs for previous threats and confirm their reputation with URL scanning tools. |
||
[Blank] |
The message has a primary override applied in policy. |
Conduct a comprehensive cross-section review of Email Details, Quarantine Details, URLs, and Attachments. |
||
Resolve Normal-Urgency Alerts
Not all alerts or incidents require investigation or escalation. Normal‑urgency alerts reflect expected operational behavior and are typically resolved through acknowledgement. When applicable, minimal action may be taken by the security team without the need for further analysis or investigation.
Alert/Incident Name |
Description |
Response |
Admin submission result completed |
If an Admin Submission completes the rescan of a submitted entity, an alert will be generated. |
Acknowledge this action may mean a revisit to the initial reason for submission, or confirmation of actions already taken, and resolve the alert. |
Email reported by user as junk |
When a user reports an email as junk using the built-in report button in Outlook, an alert is generated and a entry is created in the user submissions queue. Users will be expecting analysis and feedback on their submission. |
Respond by following the guidance for monitoring and responding via the Monitor & Respond: Email User Submissions Queue operation in addition to resolving the alert. |
Email reported by user as malware or phish |
When a user reports an email as malware/phishing using the built-in report button in Outlook, an alert is generated, and an entry is created in the user submissions queue. Users will be expecting analysis and feedback on their submission. |
Respond by following the guidance for monitoring and responding via the Monitor & Respond: Email User Submissions Queue operation in addition to resolving the alert. |
Email reported by user as not junk |
When a user reports an email as not junk using the built-in report button in Outlook, an alert is generated and a entry is created in the user submissions queue. Users will be expecting analysis and feedback on their submission. |
Respond by following the guidance for monitoring and responding via the Monitor & Respond: Email User Submissions Queue operation in addition to resolving the alert. |
User requested to release a quarantined message |
A user has requested the release of a message that was quarantined by an administrator release level policy. This action generates an alert, and the message will need to be decided upon by an administrator. |
Respond by following the guidance for monitoring and responding via the Monitor & Respond: Email Quarantine Queue operation in addition to resolving the alert. |
Tenant Allow/Block List entry is about to expire |
If an allow or block entry in the Tenant Allow/Block List is approaching its expiration date, an alert will be generated seven days before it expires. |
Acknowledge this action requires no further attention, as the half-life of allowances are working as intended and resolve the alert. |
Email messages containing malicious file removed after delivery |
If messages containing a malicious file were delivered to mailboxes in your organization, but removed by ZAP automation before creating impact, an alert will be generated. |
Acknowledge this action requires no further attention, as the remediation has been performed automatically and resolves the alert. |
Email messages containing malicious URL removed after delivery |
If messages containing a malicious URL were delivered to mailboxes in your organization, but removed by ZAP automation before creating impact, an alert will be generated. |
Acknowledge this action requires no further attention, as the remediation has been performed automatically and resolves the alert. |
Email messages containing malware removed after delivery |
If messages containing malware were delivered to mailboxes in your organization, but removed by ZAP automation before creating impact, an alert will be generated. |
Acknowledge this action requires no further attention, as the remediation has been performed automatically and resolves the alert. |
Email messages containing phish URLs removed after delivery |
If messages containing a phishing URL were delivered to mailboxes in your organization, but removed by ZAP automation before creating impact, an alert will be generated. |
Acknowledge this action requires no further attention, as the remediation has been performed automatically and resolves the alert. |
Email messages from a campaign removed after delivery |
If messages related to a adversary campaign were delivered to mailboxes in your organization, but removed by ZAP automation before creating impact, an alert will be generated. |
Acknowledge this action requires no further attention, as the remediation has been performed automatically and resolves the alert. |
Email messages removed after delivery |
If messages were delivered to mailboxes in your organization, but removed by ZAP automation before creating impact, an alert will be generated. |
Acknowledge this action requires no further attention, as the remediation has been performed automatically and resolves the alert. |
Removed an entry in Tenant Allow/Block List |
If an allow entry in the Tenant Allow/Block List is manually removed by an administrator, an alert will be generated. |
Acknowledge this action requires no further attention, as the entry has already been removed by an administrator and resolve the alert. |
Admin triggered manual investigation of email |
If an administrator triggers a manual investigation of an email from Threat Explorer, an alert will be generated. |
Acknowledging this action may mean a revisit to the initial reason for submission, or confirmation of actions already taken. |
Creation of forwarding/redirect rule |
Notification that is received when a user configures any of the applicable mail flow rules that are geared towards forwarding or redirecting mail, these rules can be utilized in nefarious ways such as forwarding received mail to an external address or redirecting messages to a void address. |
If the rule creation does not align with an expected creation, consider determining which new forwarding rules have been created using the Investigate Transport Rules article in addition to resolving the alert. |
![]()
Remediate High-Urgency Alerts
Some alerts and incidents require additional investigation due to their potential impact on business operations or security posture. These high‑urgency alerts often involve activity that must be evaluated within the context of the organization and may rely on the judgment of a technical decision‑maker.
Alert/Incident Name |
Description |
Response |
User restricted from sending email |
An internal user has been detected of exceeding the Outbound Spam Threat Policy daily external sending limit. They will be prevented from sending any mail until they have been re-allowed or permitted via an exception. |
Respond by confirming the reason for the users' account being blocked is not related to malicious activity and re-enable sending via the Defender for Email Restricted Sender Re-Enable Action article in addition to resolving the alert. |
Email sending limit exceeded |
An internal user has been detected of exceeding the Outbound Spam Threat Policy daily external sending limit. They will be prevented from sending any mail until they have been re-allowed or permitted via an exception. |
Respond by confirming the reason for the users' account being blocked is not related to malicious activity and re-enable sending via the Defender for Email Restricted Sender Re-Enable Action article in addition to resolving the alert. |
Messages containing malicious entity not removed after delivery |
If a message was detected by the Anti-Malware Threat Policy but was still delivered to a recipient’s inbox instead of being processed to the Quarantine Queue, it is required that an administrator remove these messages manually from the affected user. |
If the message looks to be malicious, consider a manual removal of the message from the inbox in addition to resolving the alert. |
A potentially malicious URL click was detected |
If a message that has been identified by the Safe Links Threat Policy has been detected to have an embedded malicious URL housed within it after delivery and a user has clicked this link, a notification will be delivered to notify you of a potential IOC that has been initiated. |
If the URL looks to be malicious, consider determining which URLs have been clicked by the effected user via the Investigate URL Clicks article in addition to resolving the alert. |
A user clicked through to a potentially malicious URL |
If a message that has been identified by the Safe Links Threat Policy has been detected to have an embedded malicious URL housed within it and despite the warning the recipient has still clicked through to view the URL, a notification will be delivered to notify you of a potential IOC that has been initiated. |
If the URL looks to be malicious, consider determining which URLs have been clicked by the effected user via the Investigate URL Clicks article in addition to resolving the alert. |
Phish not zapped because ZAP is disabled |
For read or unread messages that are identified as phishing (not high confidence phishing) after delivery, ZAP quarantines the message that has been identified as Phishing. |
Acknowledge additional configuration of the Anti-Spam threat protection policy may need to be conducted and resolve the alert. |
Malware not zapped because ZAP is disabled |
For read or unread messages that are found to contain malware after delivery, ZAP quarantines the message that contains the malware attachment. |
Acknowledge additional configuration of the Anti-Malware threat protection policy may need to be conducted and resolve the alert. |
A Tenant Allow Block List entry has been found malicious |
An allow entry in the Tenant Allow/Block List has been detected as malicious after analysis by Microsoft. This may mean the entry should be reevaluated. |
Consider determining if the tenant allow block list entry is still necessary in addition to resolving the alert. |
Admin triggered user compromise investigation |
Alert is triggered when an administrator manually starts a user compromise investigation from Threat Explorer, targeting either an email sender or recipient. The alert does not indicate malicious activity by itself. Instead, it serves as a notification that a security administrator has initiated an investigation into a user or email as a precaution or response to suspected risk. |
Respond by reviewing the alert to confirm that a manual user compromise investigation was intentionally initiated and identify the administrator who triggered it. Using the provided link, review the scope, status, and any findings related to the email sender or recipient. |
Phish delivered due to an ETR override |
If Microsoft detects that an Exchange Transport Rule allowed the delivery of a high-confidence phishing message to a mailbox, an alert will be generated. |
Acknowledge this action is indicating a risk with an Exchange Transport Rule and resolve the alert. |
Phish delivered due to an IP allow policy |
If Microsoft detects that an IP allow rule allowed the delivery of a high-confidence phishing message to a mailbox, an alert will be generated. |
Acknowledge this action is indicating a risk with an IP allowance and resolve the alert. |
Suspicious connector activity |
If a connector that has been configured through the Exchange Admin Center has been identified as handling suspicious messages it will be restricted from sending any messages. The impact to mail flow will be dependent on the directionality specified in the connector creation. |
If the behavior does not align with expected connector behavior, consider following the guidance in the Investigate Connector Configuration article to discover more sending patterns in addition to resolving the alert. |
Suspicious Email Forwarding Activity |
Alert that is generated when a suspicious email forward is detected, this can be a redirect that points to an external address that isn’t recognized within your tenant. |
Consider determining if any new ETR's have been created recently via the Investigate Transport Rules article in addition to resolving the alert. |
Suspicious tenant sending patterns observed |
Alert that points to suspicious mail flow being generated from end users within the tenant, if this pattern is maintained for a prolonged period this could lead to all mailboxes associated with the tenant being blocked from sending emails. |
Consider determining sending patterns for the tenant as a whole via the Investigate Tenant Wide External Traffic article in addition to resolving the alert. |
Suspicious email sending patterns detected |
If an internal user is detected of sending suspicious messages outside the organization they will be monitored, and if the activity is continued for a prolonged period, they will be prevented from sending mail until remediation can be conducted on the account. |
If the behavior does not align with an expected sending pattern, consider following the guidance in the Investigate External Email Traffic article to discover more sending patterns in addition to resolving the alert. |
Reply-all storm detected |
In the case of a user initiating a reply all message on a thread tied to a large distribution list, a notification will be delivered to notify you of the possible throttling that could take place on the tied email servers. |
Consider determining the impact of the reply-all storm via the Investigate Reply-All Impact article in addition to resolving the alert. |
Messages have been delayed |
If a connector is having trouble handling a message either internally or externally facing, it will be held within a delayed message queue, if the number of delayed messages exceeds the system threshold and they have been queued for an extended period a message will be delivered to notify you of the need to investigate potential impact. |
Consider determining which emails are being held due to delays via the Investigate Mail Delivery article to communicate delays to any affected recipients in addition to resolving the alert. |
Tenant restricted from sending unprovisioned email |
Traffic from the tenant has been sent from unprovisioned domains that are housed within it, and as a result the tenant will be banned from having sending functionality applied to any of their attached mailboxes regardless of the domain name specified. |
Contacting Microsoft Support will need to be performed to remove the sending ability ban that has been enforced on the tenant in addition to resolving the alert. |
Tenant restricted from sending email |
Traffic from the tenant has been detected as suspicious for a prolonged period, and as a result the tenant will be banned from having sending functionality applied to any of their attached mailboxes. |
Contacting Microsoft Support will need to be performed to remove the sending ability ban that has been enforced on the tenant in addition to resolving the alert. |
Unusual volume of external file sharing |
Alert is triggered when a large number of files stored in SharePoint or OneDrive are shared with people outside of the organization in a short period of time. This activity may indicate accidental oversharing or potential data leakage, as external users are being given access to internal files. |
Respond by looking for signs of excessive or unexpected external sharing. If concerns are identified, escalate the incident to an administrator with the appropriate access to review sharing settings, confirm business justification, and remediate any unauthorized or risky activity. |
Form blocked due to potential phishing attempt |
Alert is triggered when the system detects activity that may indicate a phishing attempt using an online form. The behavior suggests that a form may be designed to trick users into providing sensitive information, such as login credentials or personal data. This alert helps bring attention to potentially malicious forms so they can be reviewed and validated. |
Respond by reviewing the alert details to understand why the form was flagged and identify any available indicators of suspected phishing behavior. If the activity appears suspicious or poses potential risk, the analyst should escalate the alert to an administrator with the appropriate access to review the form, assess its legitimacy, and determine whether corrective action is required. |
Form flagged and confirmed as phishing |
Alert is triggered when a form created in Microsoft Forms within your organization is reported as suspicious and later confirmed as phishing by Microsoft. The confirmation is based on abuse reports and Microsoft’s analysis, indicating that the form was likely designed to collect sensitive information through deceptive or malicious means. |
Respond by reviewing the alert details to understand which Microsoft Form was confirmed as phishing and identify the creator associated with the form. This alert represents a confirmed phishing detection, the analyst should promptly escalate the incident to an administrator with Microsoft Forms and security management access. |
User restricted from sharing forms and collecting responses |
Alert is triggered when a user in the organization is restricted from creating or sharing Microsoft Forms and collecting responses due to repeated phishing‑related behavior. The restriction is automatically applied after the system detects patterns consistent with multiple phishing attempts |
Respond by reviewing the alert details to identify the user who was restricted and understand the context of the repeated phishing‑related behavior that triggered the enforcement action. The analyst does not have access to modify Microsoft Forms settings or user restrictions, the alert should be escalated to an administrator with the appropriate permissions. |
Teams message reported by user as security risk |
Alert is triggered when a user reports a Microsoft Teams message as a potential security risk. User reports may indicate suspected phishing, malicious links, unsafe attachments, or other concerning behavior within a Teams conversation. This alert helps surface messages that users believe could pose a security threat and should be reviewed for potential risk. |
Respond by reviewing the alert details to understand which Teams message was reported, who reported it, and the nature of the suspected risk. This alert is based on user‑reported concern and the analyst does not have access to modify Teams or security configurations, the alert should be escalated to an administrator with the appropriate permissions. |
Elevation of Exchange admin privilege |
Alert that notifies administrators when a user has received the Exchange Admin role, this can be a useful IOC for possible privilege escalation or can be leveraged to track possible configuration misconfiguration due to unsanctioned user activity. |
If the role escalation does not align with an expected elevation, consider determining which user has elevated into the role and deprivileging as necessary in addition to resolving the alert. |
In the context of email alert and incident management, monitoring includes 2 steps: alert monitoring and incident monitoring.
This fact is due to the nature of the Defender alert and incident management system, wherein, alerts are the drivers for incidents. An alert contains the specifics about a point in time threat or activity, and incidents are simply one or more alerts combined together. This means a single alert has a high likelihood of generating an incident, and when an alert is remediated or resolved, the incident mirrors this status. The resulting workflow works best when working through alerts first, and then incidents, allowing the resolution of alerts to automatically solve incidents without further intervention in most cases.
Review the Defender for Email Alert Queue
Reviewing unresolved alerts is first, as it drives resolution in both alerts and incidents.
Review the Defender for Email Incident Queue
Reviewing unresolved incidents is next, as checking no further actions are required after solving for alerts in recommended.
In the context of email alert and incident management, a response action is always warranted.
This fact is due to the nature of the email alert and incident management system, wherein, automation may automatically resolve some alerts and by extension the incidents they are a part of automatically. However, alerts and incidents which are not covered under this automation will be marked as “In Progress” or “New”, and subsequently require acknowledgement and resolution at a minimum, or additional actions in certain cases.
Respond with Alert Resolved
The primary goal of alert queue management is concerned with the acknowledgement and resolution of alerts in the queue. Further investigation and response for specific alerts does not need to be performed to successfully resolve an alert, however, there are cases where those additional actions are warranted. See the “Recognize when to Investigate and Resolve” and “Recognize when to Respond and Resolve” sections for more information on these cases.
Respond with Incident Resolved
The primary goal of incident queue management is concerned with the acknowledgement and resolution of incidents in the queue. Further investigation and response for specific incidents does not need to be performed to successfully resolve an incident, however, there are cases where those additional actions are warranted. See the “Recognize when to Investigate and Resolve” and “Recognize when to Respond and Resolve” sections for more information on these cases.
Need Assistance?
Reach out to your Customer Success Manager to discuss how a Sittadel cybersecurity analyst can assist in managing these tasks for you. New to our services? Inquire about arranging a consultation to explore optimizing your Azure environment for painless management.
.png?width=190&height=95&name=Sittadel%20Header%20Logo%20(2).png)



