This admin procedure will provide background information on group creation and leveraging role distribution through groups, then will dive into a review that should be conducted on established RBAC groups configured with Security Essentials.
This article is intended for employees of organizations that use Sittadel's security. Additionally, there are some actions that can only be accomplished by those with administrative privileges.
Groups
Azure Active Directory (Azure AD) groups are used to manage users that all need the same access and permissions to resources, such as potentially restricted apps and services. Instead of adding special permissions to individual users, you create a group that applies the special permissions to every member of that group.
Azure Active Directory (Azure AD) provides several ways to manage access to resources, applications, and tasks. With Azure AD groups, you can grant access and permissions to a group of users instead of for each individual user. Limiting access to Azure AD resources to only those users who need access is one of the core security principles of Zero Trust.
Azure AD lets you use groups to manage access to applications, data, and resources. Resources can be:
- Part of the Azure AD organization, such as permissions to manage objects through roles in Azure AD
- External to the organization, such as for Software as a Service (SaaS) apps
- Azure services
- SharePoint sites
- On-premises resources
With Azure AD Premium P1 or P2, you can create role-assignable groups and assign Azure AD roles to these groups.
This feature simplifies role management, ensures consistent access, and makes auditing permissions more straightforward.
Assigning roles to a group instead of individuals allows for easy addition or removal of users from a role and creates consistent permissions for all members of the group.
You can also create custom roles with specific permissions and assign them to groups.
Why assign roles to groups?
When people join the group, they're assigned the role indirectly.
Your existing governance workflow can then take care of the approval process and auditing of the group's membership to ensure that only legitimate users are members of the group and are thus assigned the role.
Procedure Scope: Administrators
Required Group Membership: Admin.UserRole
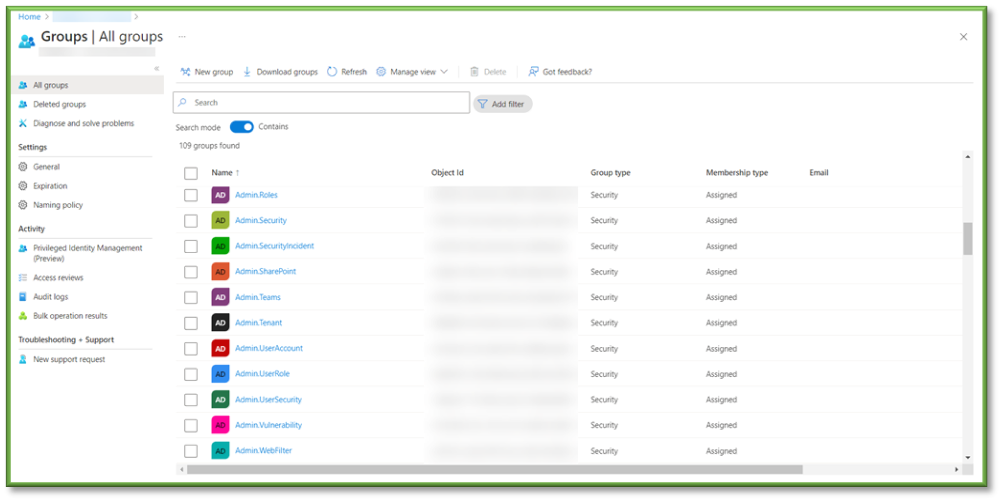
Reviewing Privileged Group Membership
- Navigate to Groups – Azure Active Directory, a list of all groups within the organization will be displayed. For this procedure, we will be focusing on administrative groups (Admin.xxx), checking for role assignments as well as users assigned to each of the groups.


- First, we will check the Membership tab located under the Manage section of the group profile. This will list all the users that have been assigned to this group, this is important in detecting user access and unnecessary privilege escalation. It will be up to you to determine the job role associated with each user and determine if they are out of scope of what the group allows role permission for or if they will need to be assigned to the group to complete their expected duties. If over privilege is detected, you will need to locate the user in the list and select Remove to remediate the misassignment. Additionally, if you determine that a user isn’t present that will need the role permissions associated with the group, you will select Add Members and provide the intended user in the search.

- Role Assignment will go hand in hand with Membership, locate the Assigned Roles tab under the Management section. This will list all the assigned roles associated with the group, detailing the type of permissions granted by the role. These values are important to keep eyes on if a discrepancy is detected in role assignment; make note of the role for questioning purposes, then select the role and select Remove Assignments to remediate the privilege creep. Additionally, you could add a role to the group if the permissions listed don’t fully fall in line of scope that the members should be able to execute; select Add Assignments and search through the directory roles to implement a wider scope of operation for the group.

You're Finished!
You should have successfully browsed through all of the configured admin groups, checking for the members of each group and whether they belong to the group depending on their role in the organization. Additionally, you want to make sure that the role assignment to each of the groups is in line with what was configured during the deployment and check for any drift in configuration. For any other problems or questions, reach out to us!
