This work instruction will allow an administrator to view details on why a specified user is experiencing sign-in failures.
This article is intended for employees of organizations that use Sittadel's security. Additionally, there are some actions that can only be accomplished by those with administrative privileges.
- Navigate to Sign-In logs – Azure Active Directory, select Add Filters, specify Status and select Apply to finalize the filter selection.

- Select the Status bubble, specify Failure and select Apply.

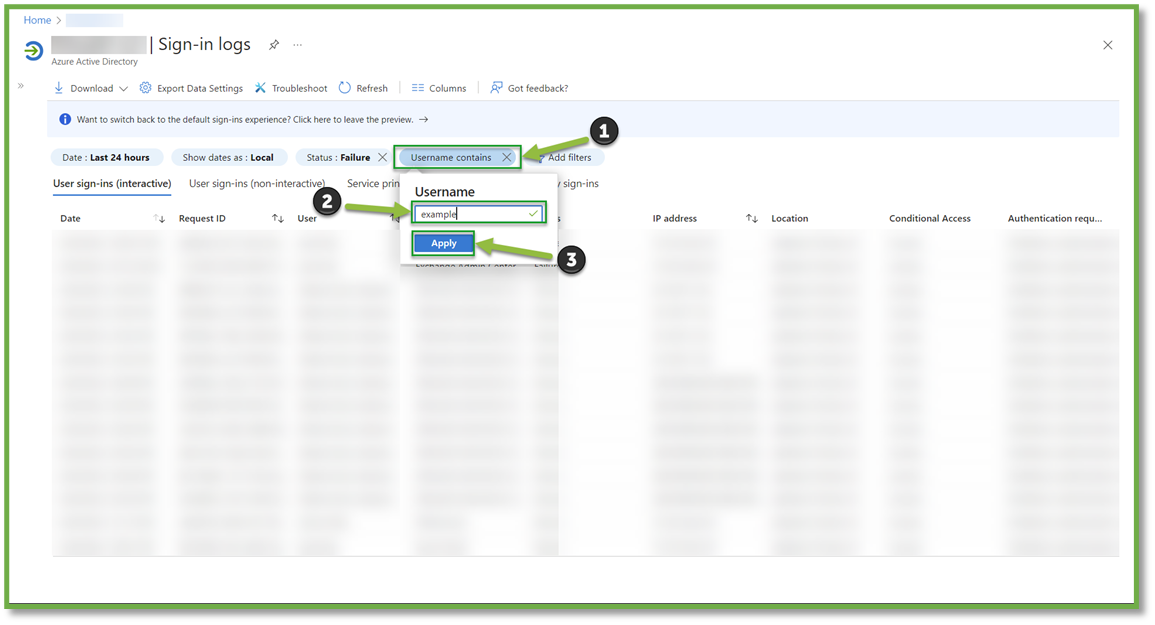
- We will also want to specify the user that is experiencing sign-in failures. Select Add Filters, specify Username and select Apply to finalize the filter selection.

- Select the Username bubble, provide the username and select Apply.
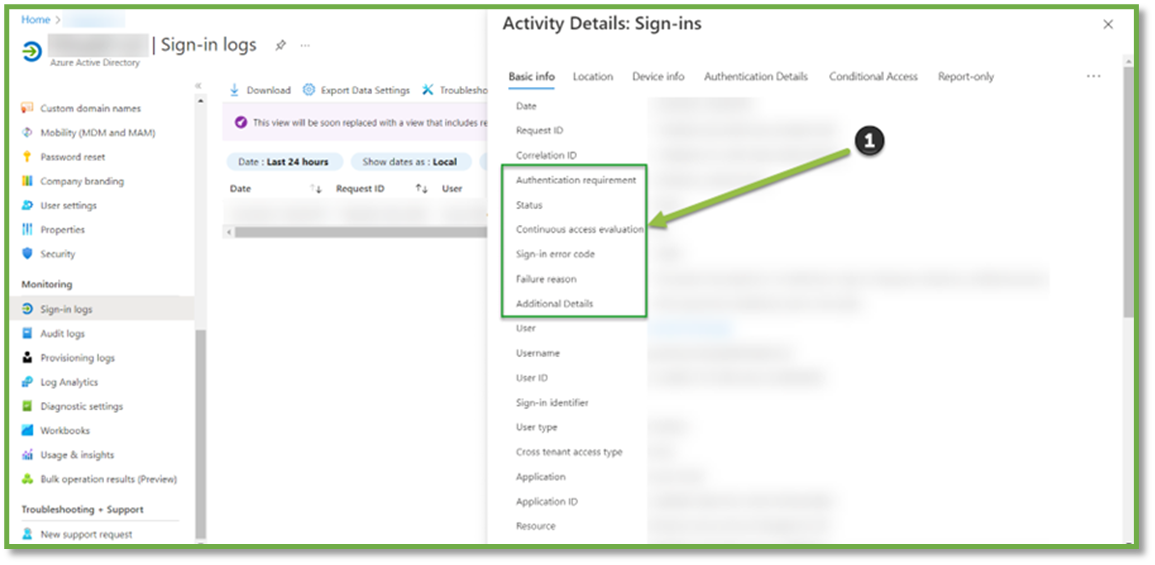
- All failed login attempts will be generated; clicking on a failure instance will generate a report which will provide details on why access was denied.
You're Finished!
You should have successfully located the sign-in failures tied to the specified user account and began analyzing possible solutions to alleviate the failure from event details. For any other problems or questions, reach out to us!
