User Sign-In Log Report
This guide will show an administrator how to view sign-in activities related to platforms that utilize users Microsoft account for authentication.
 Role Requirements
Role Requirements
Procedure Scope: Administrators
Required Group Membership: Admin.Compliance
![]()
-
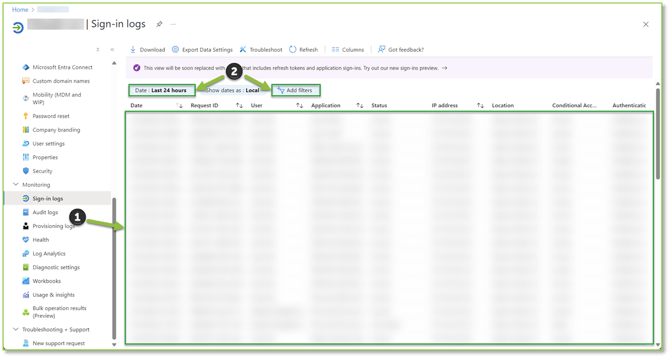
Navigate to the Sign-In Logs – Azure Active Directory portal, here you will find all authentication attempts into a Microsoft Entra tenant, which includes your internal apps and resources. From this page you will be able to identify sign-in errors and patterns that will provide valuable insight into how your users access applications and services. Additionally, you will be able to describe the activity associated with an authentication attempt by identify details such as who is performing the sign-in (the identity of the associated User or Service Principal), what resource is attempting to be accessed by the identity, etc. Filtering can be adjusted if you know specific information related to the event you are trying to explore.
Need Assistance?
Reach out to your Customer Success Manager to discuss how a Sittadel cybersecurity analyst can assist in managing these tasks for you. New to our services? Inquire about arranging a consultation to explore optimizing your Azure environment for painless management.
.png?width=190&height=95&name=Sittadel%20Header%20Logo%20(2).png)